An IP address grabber or IP Logger serves as a tool or software created to acquire the unique identifier associated with a user’s device when connected to the internet, known as the IP address.
The functioning of IP grabbers involves the transmission of a link or message to the user, and upon clicking, the program captures the user’s IP address.
These tools find application in diverse scenarios, such as monitoring online activities, pinpointing a user’s geographical location, or initiating a DDoS attack. Cybercriminals frequently employ IP grabbers for illicit purposes like identity theft, phishing scams, and hacking.
It is crucial for internet users to recognize the potential dangers linked with IP grabbers and implement measures to safeguard their online privacy and security.
What are IP Address Grabbers?
IP address grabbers, also known as IP address trackers and IP loggers, essentially refer to the same concept under different names. These online services enable the creation of fully traceable URLs.
To utilize these services, one simply needs to share the link and persuade the recipient to click on it. Clicking the link provides the user with the IP details of the person.
Such services are commonly employed to obtain a person’s IP address or location without their awareness. Certain IP tracker services utilize advanced technologies to accurately determine the location of the device where the link was clicked. Despite their legitimate uses, IP loggers are sometimes misused.
How Do IP Grabbers Work?
An IP grabber stands as an external service enabling internet users to create a link that identifies the IP address of any individual.
The process involves having the intended target click on the generated link. While top-notch IP grabbers can be beneficial, they have also become a valuable tool for individuals with malicious intentions.
Cybercriminals often target specific individuals, aiming to lure them into clicking on fake links generated by IP grabbers.
To safeguard your address, it is imperative not to click on unverified links. Fortunately, several websites offer tools to check the safety of a link in case of suspicion.
IP addresses serve as the exclusive means through which devices communicate with the internet. While they do not pinpoint a specific device, address, or precise location, they function as tools for tracking online users.
Determining the exact location of a web user through an IP address proves challenging; at best, it provides information about the country or city. These addresses represent general information, akin to public credentials.
It’s important to note that a single IP address might be shared by thousands of internet users. Despite this, the actions of cybercriminals, who may not need precise location details but seek clues for online fraud, remain unjustifiable.
Uncovering your IP address could potentially reveal the city you are in, and when coupled with other details, this information may be exploited for illegal activities such as impersonation and fraudulent loan applications.
Why Are IP Loggers Links Privacy and Security Risks?
Each device is equipped with its router, housing an Internet Protocol Address that functions as an identifier facilitating communication between your device and the computer.
While these identifiers are integral, there is no need for undue concern as obtaining them holds minimal real-world rewards.
In the event someone endeavors to pilfer your IP address, the potential consequences are generally limited to harmless pranks or inconveniences in your browsing experience. The impact of IP addresses is not as dire as it may seem.
However, it’s crucial to recognize that your IP address is considered a confidential credential. While most websites store it for their databases, they typically utilize it for business-to-business (B2B) purposes and to enhance user services.
Outlined below are three ways in which IP grabber links can be exploited by malicious actors to intrude upon your private space:
1. Uncovering Your Geographical Location
Your IP address has the capacity to disclose your location, ranging from broad details like your country and state to, in rare instances, pinpointing your exact neighborhood.
While this may hold little significance for most internet users, it serves as a red flag for a select few. Consider the scenario of a stranger possessing information about your location and Internet Service Provider (ISP) directly derived from your address.
IP grabbing facilitates the identification of the ISP for virtually anyone. While this information may appear rudimentary, it holds value for criminals when combined with other private details.
2. Restricting Access to Numerous Websites
Imagine attempting to engage in an online game only to encounter a pop-up notification stating, ‘Access denied.’
In such instances, the sole reason for this hindrance is likely that your IP address does not meet the eligibility criteria for accessing the game.
This limitation extends to general web browsing, where websites may block your access to their content.
It’s a two-way street, as scammers might employ this tactic to impede actions that could disrupt their illicit activities. If there’s any doubt about the legitimacy of a website, it is advisable to exit promptly.
While reputable websites often restrict access based on IP location, some malicious ones aim to engage in unlawful activities. In such cases, immediate preventive measures are warranted.
3. Performing a Denial of Service Attack (DoS)
While Denial of Service (DoS) attacks are commonly directed at prominent companies with extensive databases, ordinary internet users should understand their potential impacts.
These attacks disrupt network connections by inundating them with excessive data, thereby blocking regular traffic. Cybercriminals may resort to a DoS attack when they wish to prevent your engagement with a specific site.
Performing such an attack requires obtaining the IP addresses of targeted individuals, and if your IP address is accessible, the execution of this illegal act becomes significantly easier. To mitigate risks, it is advisable to limit your online activities to reputable websites.
Are IP Grabber Links legal?
Using IP grabber links with the intention of capturing someone’s IP address without their consent can raise legal and ethical concerns.
The legality of IP grabber links depends on how they are used and the intentions behind their deployment.
If someone uses an IP grabber link for legitimate and legal purposes, such as tracking and securing their own network, monitoring authorized users, or troubleshooting technical issues with explicit consent, it may be considered legal.
However, using IP grabber links with malicious intent, such as for cyber attacks, hacking, stalking, or any unauthorized and harmful activities, is likely to be illegal.
In many jurisdictions, unauthorized access to someone’s personal information, including their IP address, without their consent, can be considered an invasion of privacy and a violation of computer security laws.
8 Best IP Grabbers to Use
Here are the Best IP Logger Services Available on the Web
1. SoftPerfect Network Scanner
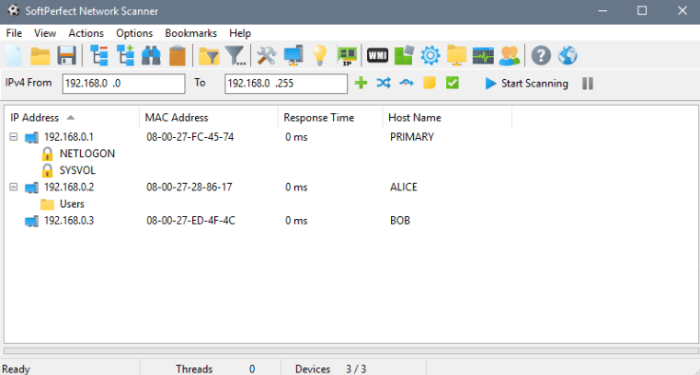
SoftPerfect Network Scanner is a valuable utility for enhancing the efficiency of computer network management.
Tailored to scan both IPv4 and IPv6 networks, this tool offers a comprehensive set of features to streamline network support procedures.
By utilizing SoftPerfect Network Scanner, you can identify devices connected to your network through a ping sweep, verifying their online status and displaying real-time results.
The scanner excels in detecting the hardware MAC addresses of devices, even if they are situated across routers, facilitating device identification and tracking based on their physical addresses.
This tool is good at retrieving diverse information about network devices. It can collect system data through protocols like WMI, remote registry, file system, and service manager.
Additionally, the scanner is adept at scanning for open TCP ports, certain UDP services, and SNMP services, aiding in the identification of network services running on devices.
SoftPerfect Network Scanner transcends basic network scanning by providing advanced functionalities. It can uncover shared folders, including both writable and hidden ones on network devices, simplifying the management and access of shared resources.
Moreover, the tool enables the execution of remote commands through SSH, PowerShell, or VBScript, empowering users to perform actions on remote devices.
Supporting Wake-On-LAN, it allows for the remote waking up of devices and offers options for remote shutdown and sending network messages.
For streamlined data analysis and sharing, SoftPerfect Network Scanner facilitates the export of scan results in various formats such as HTML, XML, JSON, CSV, and TXT.
Its seamless integration with Nmap, a widely used network scanning tool, enhances its capabilities for OS discovery and vulnerability testing.
2. Grabify
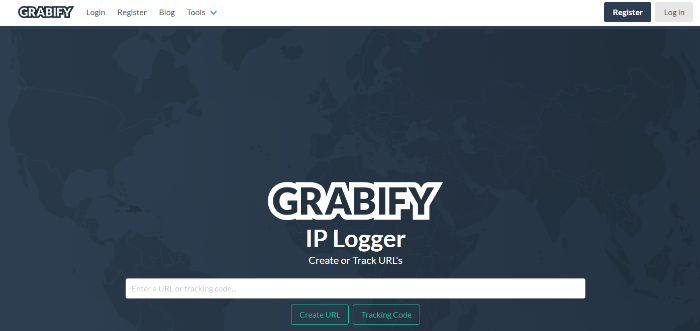
Currently dominating the market, Grabify stands out as the most widely used IP address grabber. This tool facilitates the retrieval of someone’s IP address through a simple clickable link. Once the targeted individual clicks on the link, you gain access to the details conveniently displayed on the Grabify dashboard.
An additional noteworthy feature of Grabify is the Smart Logger, which enhances your capability to capture more details about the user’s device.
This includes information such as battery life, charging status, device orientation, screen orientation, and more, although the necessity for such extensive data may be limited. The Results section of Grabify operates seamlessly, displaying a timestamp and furnishing details about the User Agent.
To pinpoint the exact location, a brief wait may be required, but for those unwilling to wait, copying the IP address for use in another IP analyzer tool is a viable option.
3. SpyLink
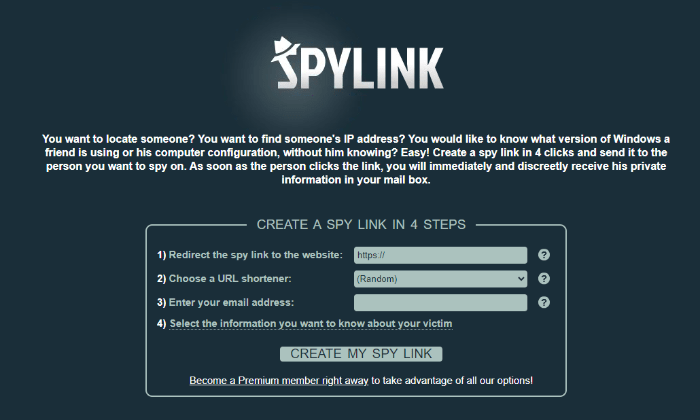
While SpyLink may not enjoy widespread popularity, it remains a top-tier option among IP address grabbers available today. To utilize this service, users are required to generate a spy link and dispatch it to the target individual.
Upon the recipient clicking on the link, SpyLink promptly furnishes the sender with the person’s confidential information, conveniently delivered to their mailbox. Clicking on the link enables SpyLink to retrieve not only the IP address but also the geographical location of the device.
Additionally, SpyLink provides a comprehensive array of details, including APN, proxy setup, browser name, cookies activation status, flash version, operating system, device screen resolution, and more.
4. IP Logger
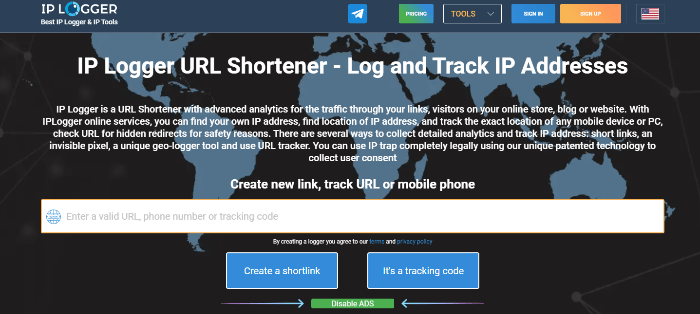
IP Logger, a web-based service, empowers users to monitor the IP addresses of individuals who engage with a specific link they create.
The process involves generating a condensed link that can be shared, and when clicked, IP Logger records the visitor’s IP address and gathers details about their device, including the browser and location.
The tracking service offers comprehensive analytics and metrics, presenting users with insights into logged IP addresses and associated data such as countries, cities, and browsers.
This information proves valuable for understanding audience demographics and shaping marketing strategies accordingly.
An additional beneficial feature is the ability to choose different types of URLs for links, providing flexibility in distribution. IP Logger includes an export function, simplifying the extraction of collected data for further analysis or marketing applications.
When it comes to functioning, this IP grabber utilizes advanced analytics to scrutinize link traffic and pinpoint the precise location of devices that interact with them.
To ensure information accuracy, it employs a secure method for checking URL redirects without revealing the user’s own IP address.
5. ps3CFW.com IP Logger
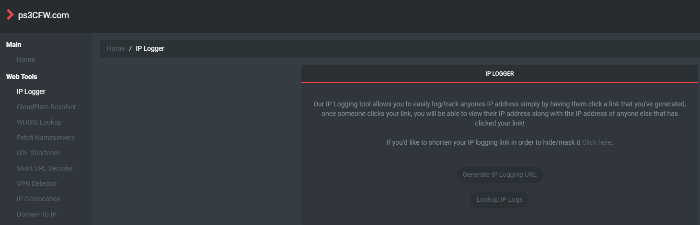
If you’re searching for a straightforward IP address logger, ps3CFW.com IP Logger presents itself as a user-friendly option, especially for those who prefer simplicity over advanced features.
This uncomplicated IP grabber operates by sending a link to the target user, and upon clicking, you promptly receive their IP address.
However, it’s worth noting that ps3CFW.com IP Logger does not provide additional details such as device type or location. For a more comprehensive understanding of the IP address, users may need to resort to third-party IP details grabber sites.
In addition to its IP tracking function, ps3CFW.com IP Logger offers other tools, including WHOIS Lookup, Cloudflare Resolver, VPN Detection, IP Ping Test, and more.
6. B-Labs Bopup Scanner
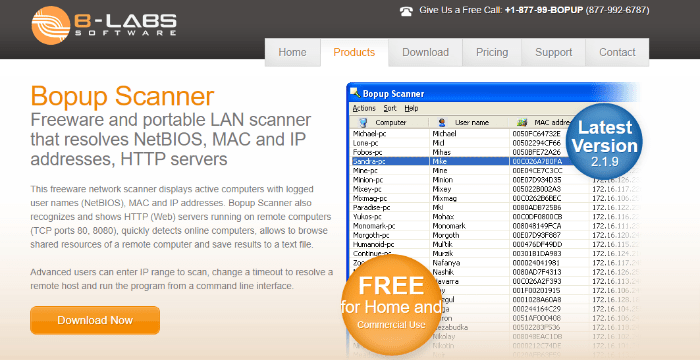
Bopup Scanner stands out as a widely embraced intranet IP scanner, functioning as a comprehensive tool for network administration.
Developed by B-Labs, known for their expertise in messaging systems, Bopup Scanner inherits this proficiency. Notably, this tool boasts high popularity due to its complete portability, enabling direct execution from a flash drive without the need for installation on your workstation.
The array of capabilities offered by Bopup Scanner aligns with expectations for an intranet IP scanner. It efficiently resolves NetBIOS, providing IP addresses, MAC addresses of connected devices, hostnames, and more. Network administrators can also assess web server status and the responsiveness of devices.
Facilitating IP configuration checks, the tool allows users to input a range of IP addresses and scrutinize each host for network shares.
An innovative feature includes the ability to set response timeouts, preventing unresponsive IP addresses from impeding the overall scanning process.
Moreover, the tool’s portability allows seamless movement between multiple workstations, empowering users to monitor network configurations from any preferred workstation.
7. Bit.ly
Bit.ly stands out as one of the top URL-shortening tools currently dominating the market, with its analytics capabilities being the key factor in its prominence on this list.
Functioning as an internet IP tracker, Bit.ly allows for the convenient sharing of shortened links across various distribution channels, including social media, online campaigns, and affiliate products.
The analytics tool empowers webmasters to monitor IP addresses, track the number of clicks, delve into user demographics, and analyze geographical statistics.
A standout feature of Bit.ly lies in its robust link management functionality. Users can generate numerous shortened links, and Bit.ly provides comprehensive information for each link, encompassing details such as the number of clicks, click origin, and user demographics.
Moreover, Bit.ly introduces an innovative feature enabling the creation of QR codes for shortened links. These QR codes can be customized with brand logos, colors, and more, presenting a versatile tool for marketing purposes.
8. Advanced IP Scanner
This intranet IP tracking tool is tailored for Windows operating systems and currently ranks among the most widely used IP scanners.
Advanced IP Scanner serves the primary purpose of correlating IP configurations with database information. You can input a range of IP addresses from a text file, and the tool provides responses following a comprehensive network scan.
The tool furnishes detailed information, encompassing IP addresses, device manufacturers, network interface vendors, MAC addresses, and hostnames.
Additional features benefit network administrators, including the ability to check device status and remotely manage workstations through RDP and Radmin functionality.
Among its additional capabilities, Advanced IP Scanner includes a popular feature—providing a list of accessible network shares, accessible with a simple click on the workstation report.
9. xResolver
xResolver is an online tool used as an IP logger. It is designed to convert Xbox and Playstation usernames into IP addresses and vice versa. This tool has been controversial and lies in the legal grey area. Using tools like xResolver to negatively impact the gaming platform is illegal. Therefore, it is important to use that tool responsibly.
In a Nutshell
Recognizing the IP addresses of those engaging with your online content has grown increasingly crucial.
These tools serve as a valuable resource, offering insights into the demographics and locations of your visitors, and enabling precise marketing strategies.
Leveraging the ability to track IP addresses, analyze traffic patterns, and monitor user engagement opens up a realm of possibilities for enhancing online presence.
Whether optimizing marketing campaigns or fortifying website security, IP grabbers provide significant advantages for both businesses and individuals.
Furthermore, these tools contribute to safeguarding personal privacy by eliminating potential threats and identifying suspicious activities.
If you've any thoughts on What is IP Grabber: Safety | Legality | Best IP Grabbers, then feel free to drop in below comment box. Also, please subscribe to our DigitBin YouTube channel for videos tutorials. Cheers!